Safeguard Policies (Preview Feature)¶
Note: This feature is in private beta. Please contact Okera for more information.
How Do Safeguard Policies Work?¶
Safeguard policies do not grant access to data. Instead they act as a global defense check or safeguard to ensure that certain data is always masked, or only allowed to be viewed by certain users, regardless of lower-level permissions granting access to it. For example, you might want to ensure that highly sensitive data, such as social security numbers, are always masked, or you might have to comply with a regionally specific regulation stipulating that customer data from that region can only be viewed by analysts in that region.
Who Do Safeguard Policies Apply To?¶
Safeguard policies apply to all users, except for catalog admins. This means that a user can have ALL on a dataset, but will still see data masked as per a safeguard policy.
How Do Safeguard Policies Interact With Existing Permissions?¶
Safeguard policies are applied after the initial permission evaluation. They always override any other transformation policies on the data, and apply, in addition, to any existing row-level filters.
For example, if a user had access to a table with a policy condition tokenizing social security numbers (SSN), but the safeguard policy masks SSN, they would see SSN masked.
Who Has Access to Control Safeguard Policies?¶
- Only catalog admins have access to create and modify safeguard policies.
- Users who can grant permissions on data objects can view (but not modify) all the safeguard policies applied across the catalog.
Activate Safeguard Policies¶
To activate safeguard policies in your Okera installation, the following configuration properties must be set to true in your Okera cluster. After adding them, contact your Okera representative for additional activation steps.
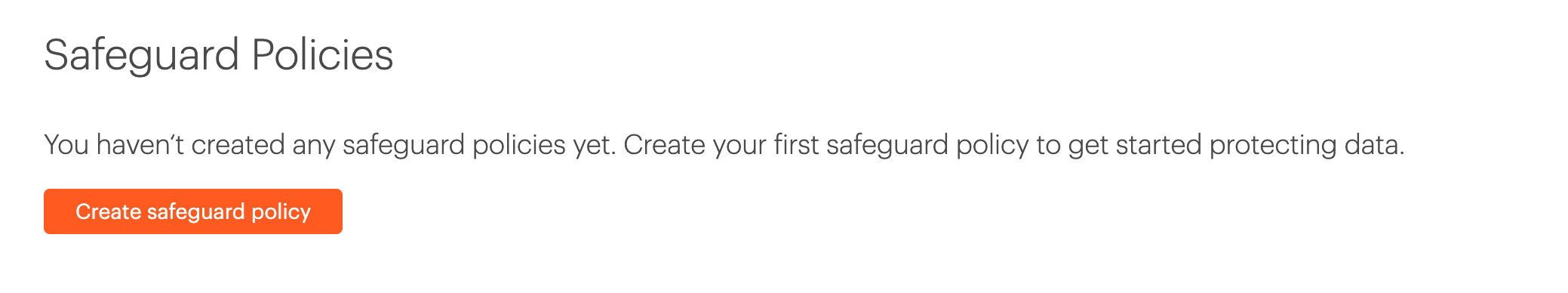
Create a Safeguard Policy¶
To create a safeguard policy, select Safeguards in the left navigation menu, and select the Create safeguard policy button.
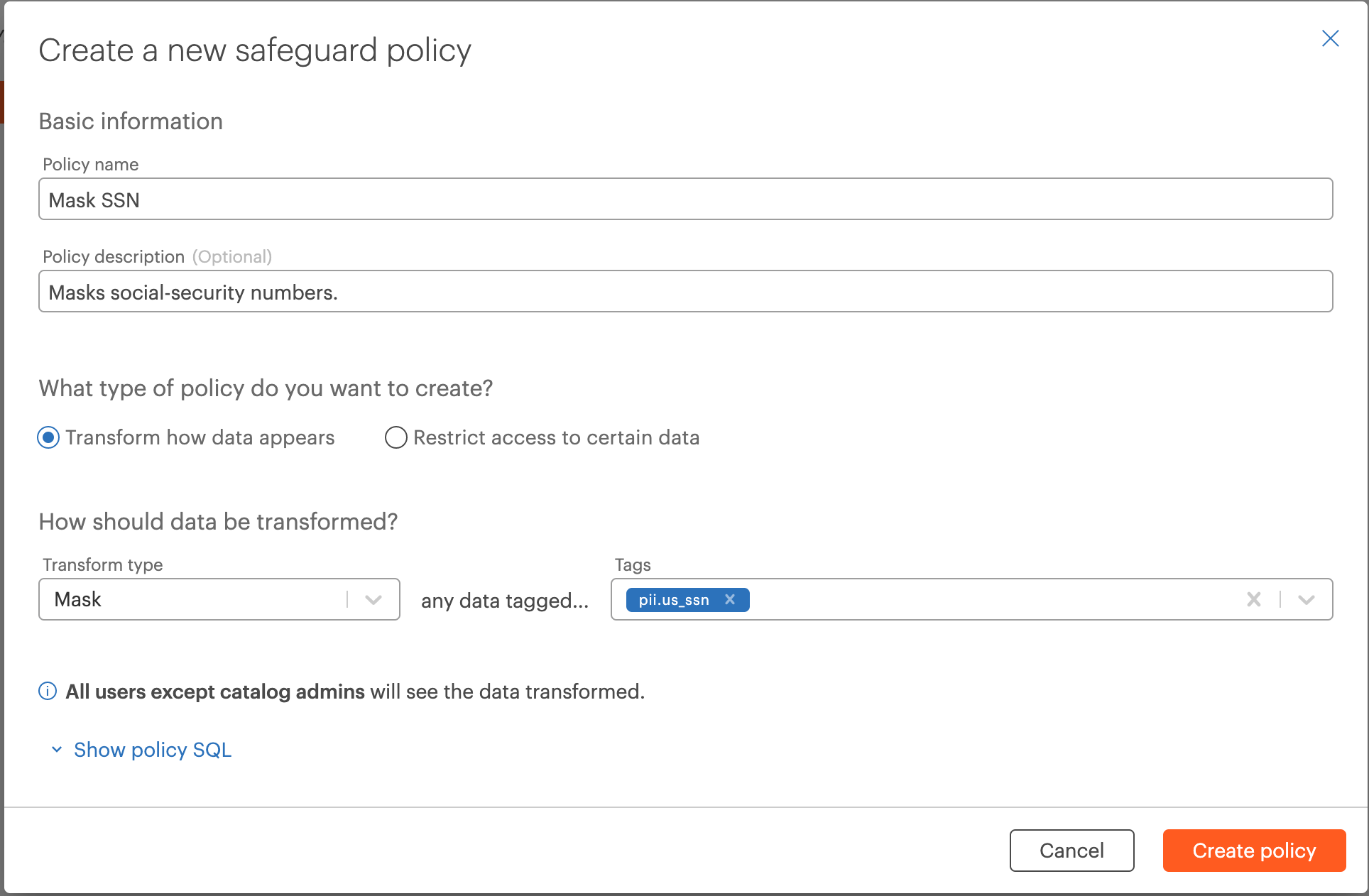
Example: Transform Data by Tags¶
The safeguard policy below ensures that any data tagged pii.us_ssn always appears masked across the entire catalog, for all users except catalog admins.
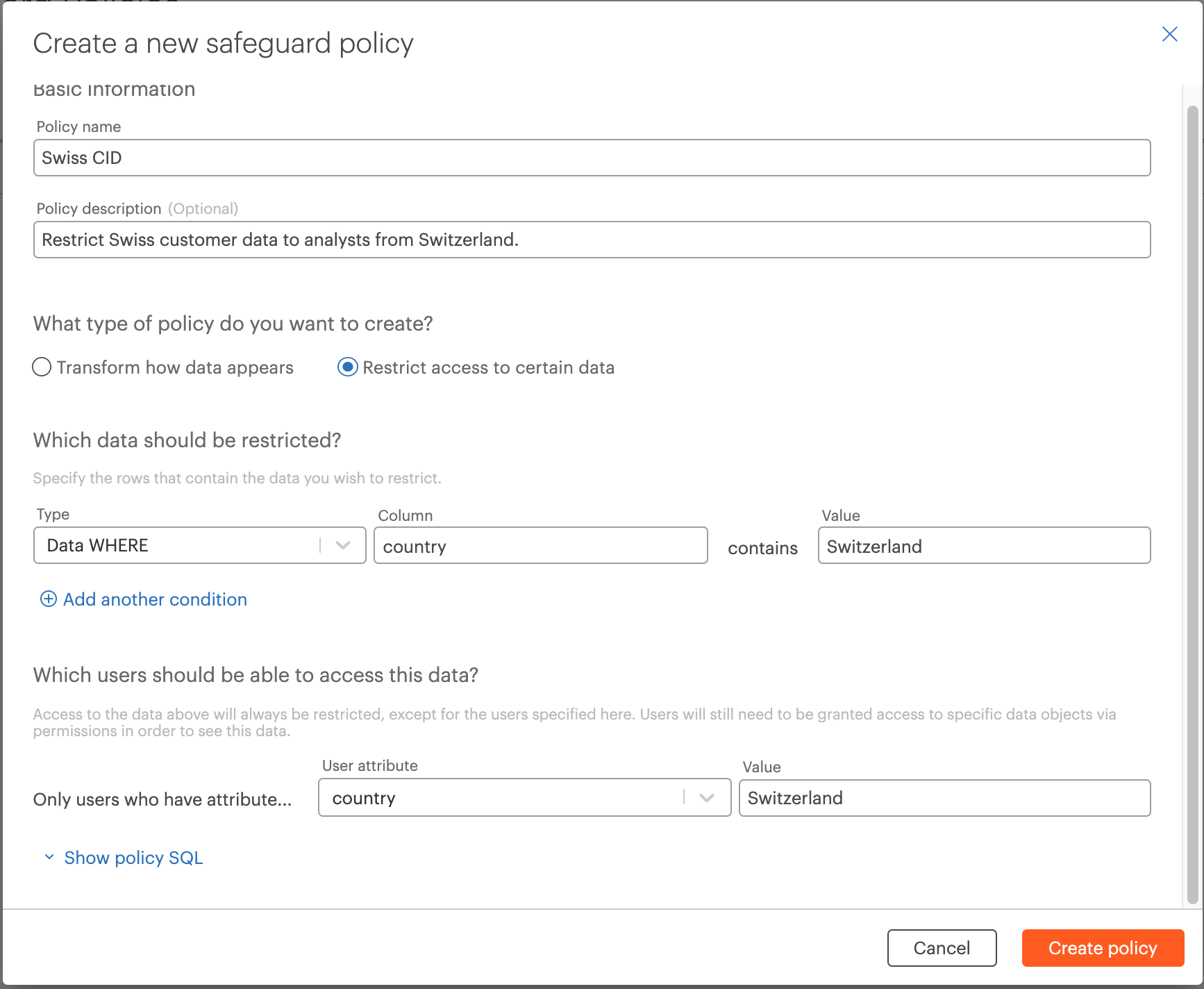
Example: Restrict Rows to Users With a Specific Attribute¶
The safeguard policy below ensures that all rows where the column country contains the value Switzerland are restricted to only users who have the user attribute Switzerland for country.
Delete a Safeguard Policy¶
Select the Delete button under Actions on the list of safeguard policies.
Warning
Deleting a safeguard policy could leave highly sensitive data exposed across the catalog and should be done with caution. Before deleting a safeguard policy, ensure that highly sensitive data will not be able accessible via lower-level permissions on databases and datasets.
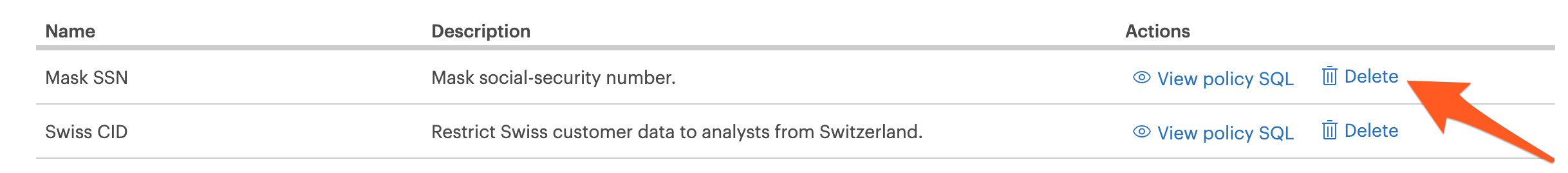
View Policy SQL¶
To programmatically create safeguard policies, you can view the associated policy SQL by selecting the Show policy SQL button during policy creation, or by selecting the View policy SQL button on the safeguard policy list.
Viewing Safeguard Policies When Granting Permissions¶
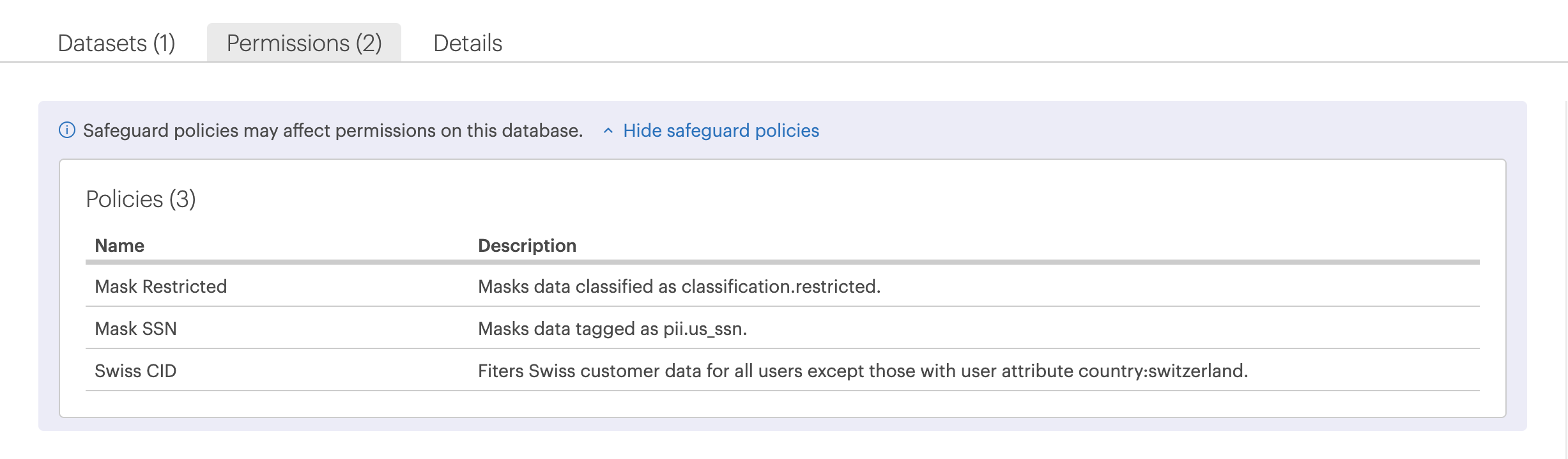
Users with access to grant permissions on data objects can see a list of all the active safeguard policies across the catalog in the policy builder as well as on the Permissions tab on the data object page. Select  to see a drop-down list of the safeguard policies defined for the entire catalog. Select
to see a drop-down list of the safeguard policies defined for the entire catalog. Select  to hide the list.
to hide the list.
FAQs & troubleshooting¶
How do safeguard policies work with different datatypes?¶
Safeguard policies are able to mask data across datatypes, see Privacy and Security Functions for more information.
What conflicts apply to safeguard policies?¶
You will not be allowed to create a safeguard policy that contradicts another safeguard policy, for example if one safeguard policy is saying mask social-security number, but another one says to null it.